

SUBSCRIBE TO OUR FREE NEWSLETTER
Daily news & progressive opinion—funded by the people, not the corporations—delivered straight to your inbox.
5
#000000
#FFFFFF
To donate by check, phone, or other method, see our More Ways to Give page.


Daily news & progressive opinion—funded by the people, not the corporations—delivered straight to your inbox.
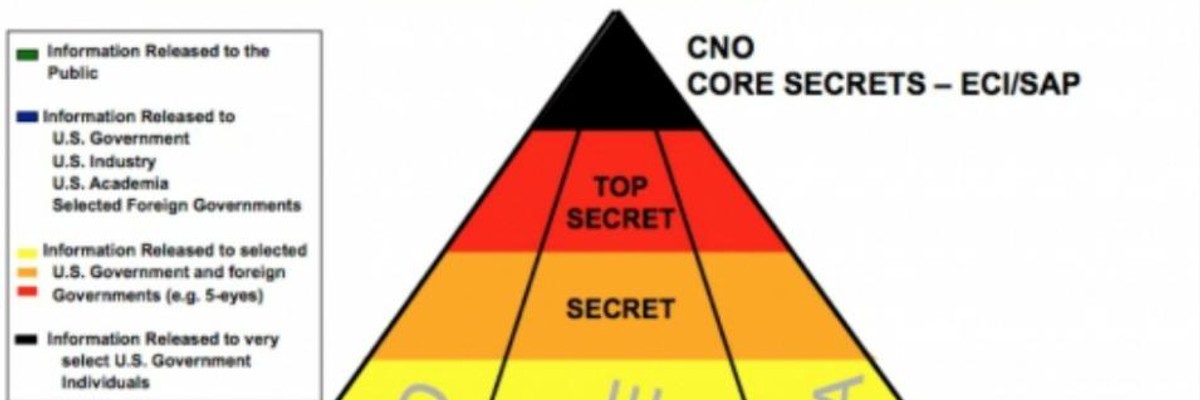
Leaked by NSA whistleblower Edward Snowden, documents indicate that the agency has used "under cover" operatives to gain access to sensitive data and systems in the global communications industry. (Image: Screenshot of top secret NSA slide)
The National Security Agency has had agents in China, Germany, and South Korea working on programs that use "physical subversion" to infiltrate and compromise networks and devices, according to documents obtained by The Intercept.
The documents, leaked by NSA whistleblower Edward Snowden, also indicate that the agency has used "under cover" operatives to gain access to sensitive data and systems in the global communications industry, and that these secret agents may have even dealt with American firms. The documents describe a range of clandestine field activities that are among the agency's "core secrets" when it comes to computer network attacks, details of which are apparently shared with only a small number of officials outside the NSA.
"It's something that many people have been wondering about for a long time," said Chris Soghoian, principal technologist for the American Civil Liberties Union, after reviewing the documents. "I've had conversations with executives at tech companies about this precise thing. How do you know the NSA is not sending people into your data centers?"
Previous disclosures about the NSA's corporate partnerships have focused largely on U.S. companies providing the agency with vast amounts of customer data, including phone records and email traffic. But documents published today by The Intercept suggest that even as the agency uses secret operatives to penetrate them, companies have also cooperated more broadly to undermine the physical infrastructure of the internet than has been previously confirmed.
Read the complete reporting at The Intercept.
Trump and Musk are on an unconstitutional rampage, aiming for virtually every corner of the federal government. These two right-wing billionaires are targeting nurses, scientists, teachers, daycare providers, judges, veterans, air traffic controllers, and nuclear safety inspectors. No one is safe. The food stamps program, Social Security, Medicare, and Medicaid are next. It’s an unprecedented disaster and a five-alarm fire, but there will be a reckoning. The people did not vote for this. The American people do not want this dystopian hellscape that hides behind claims of “efficiency.” Still, in reality, it is all a giveaway to corporate interests and the libertarian dreams of far-right oligarchs like Musk. Common Dreams is playing a vital role by reporting day and night on this orgy of corruption and greed, as well as what everyday people can do to organize and fight back. As a people-powered nonprofit news outlet, we cover issues the corporate media never will, but we can only continue with our readers’ support. |
The National Security Agency has had agents in China, Germany, and South Korea working on programs that use "physical subversion" to infiltrate and compromise networks and devices, according to documents obtained by The Intercept.
The documents, leaked by NSA whistleblower Edward Snowden, also indicate that the agency has used "under cover" operatives to gain access to sensitive data and systems in the global communications industry, and that these secret agents may have even dealt with American firms. The documents describe a range of clandestine field activities that are among the agency's "core secrets" when it comes to computer network attacks, details of which are apparently shared with only a small number of officials outside the NSA.
"It's something that many people have been wondering about for a long time," said Chris Soghoian, principal technologist for the American Civil Liberties Union, after reviewing the documents. "I've had conversations with executives at tech companies about this precise thing. How do you know the NSA is not sending people into your data centers?"
Previous disclosures about the NSA's corporate partnerships have focused largely on U.S. companies providing the agency with vast amounts of customer data, including phone records and email traffic. But documents published today by The Intercept suggest that even as the agency uses secret operatives to penetrate them, companies have also cooperated more broadly to undermine the physical infrastructure of the internet than has been previously confirmed.
Read the complete reporting at The Intercept.
The National Security Agency has had agents in China, Germany, and South Korea working on programs that use "physical subversion" to infiltrate and compromise networks and devices, according to documents obtained by The Intercept.
The documents, leaked by NSA whistleblower Edward Snowden, also indicate that the agency has used "under cover" operatives to gain access to sensitive data and systems in the global communications industry, and that these secret agents may have even dealt with American firms. The documents describe a range of clandestine field activities that are among the agency's "core secrets" when it comes to computer network attacks, details of which are apparently shared with only a small number of officials outside the NSA.
"It's something that many people have been wondering about for a long time," said Chris Soghoian, principal technologist for the American Civil Liberties Union, after reviewing the documents. "I've had conversations with executives at tech companies about this precise thing. How do you know the NSA is not sending people into your data centers?"
Previous disclosures about the NSA's corporate partnerships have focused largely on U.S. companies providing the agency with vast amounts of customer data, including phone records and email traffic. But documents published today by The Intercept suggest that even as the agency uses secret operatives to penetrate them, companies have also cooperated more broadly to undermine the physical infrastructure of the internet than has been previously confirmed.
Read the complete reporting at The Intercept.